Unlocking the Secrets of Wed to Seal: A Comprehensive Guide to Achieving Streamlined Email Security

4.7 out of 5
| Language | : | English |
| File size | : | 732 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 141 pages |
| Lending | : | Enabled |
| Screen Reader | : | Supported |
In today's digital landscape, email has become an indispensable tool for communication and collaboration. However, the rise of cyber threats has made it imperative for organizations to prioritize email security measures to protect sensitive data and ensure compliance with regulations. Wed to Seal emerges as a robust email security solution that addresses these challenges head-on, providing organizations with a comprehensive suite of features to safeguard their email communications.
Benefits of Wed to Seal
Wed to Seal offers a myriad of benefits that make it an ideal choice for organizations seeking to enhance their email security posture:
- Data protection: Wed to Seal employs advanced encryption algorithms to protect sensitive data in emails, ensuring that it remains confidential even if intercepted.
- Compliance: The solution assists organizations in meeting compliance requirements such as GDPR, HIPAA, and PCI DSS by providing features like data encryption, digital signatures, and audit trails.
- Email authentication: Wed to Seal utilizes email authentication protocols such as SPF, DKIM, and DMARC to prevent spoofing and phishing attacks.
- Email threat protection: The solution incorporates advanced threat detection mechanisms to identify and block malicious emails, including spam, viruses, and ransomware.
- Simplified management: Wed to Seal provides a centralized dashboard for easy management and monitoring of email security policies, reducing the administrative burden on IT teams.
Features of Wed to Seal
Wed to Seal's comprehensive feature set empowers organizations to achieve unparalleled email security:
- Email encryption: Wed to Seal encrypts emails using industry-standard encryption algorithms, ensuring that sensitive data is protected during transmission and storage.
- Digital signatures: The solution allows users to digitally sign emails, providing proof of authenticity and integrity, and ensuring that emails have not been tampered with.
- Email authentication: Wed to Seal supports various email authentication protocols such as SPF, DKIM, and DMARC, which help prevent email spoofing and phishing attacks.
- Threat protection: The solution incorporates advanced threat detection mechanisms to identify and block malicious emails, including spam, viruses, and ransomware.
- Policy management: Wed to Seal provides a centralized dashboard for managing email security policies, allowing organizations to tailor security settings to their specific needs.
- Reporting and monitoring: The solution offers comprehensive reporting and monitoring capabilities, enabling organizations to track email security incidents and measure the effectiveness of their security measures.
How to Implement Wed to Seal
Implementing Wed to Seal is a straightforward process that can be completed in a few simple steps:
- Sign up for a Wed to Seal account: Visit the Wed to Seal website and create an account to access the solution's features.
- Configure your email server: Follow the instructions provided by Wed to Seal to configure your email server to use the solution's encryption and authentication services.
- Install the Wed to Seal client: Install the Wed to Seal client on your email client (e.g., Outlook, Gmail) to enable encryption and digital signing of emails.
- Set up email security policies: Configure Wed to Seal's policy management dashboard to define the desired level of email security for different users and groups.
- Monitor and maintain: Regularly monitor the Wed to Seal dashboard to track email security incidents and ensure that the solution is functioning optimally.
Wed to Seal is a comprehensive email security solution that empowers organizations to safeguard their email communications, protect sensitive data, and meet compliance requirements. Its robust feature set, ease of implementation, and affordable pricing make it an ideal choice for organizations of all sizes seeking to enhance their email security posture. By implementing Wed to Seal, organizations can mitigate cyber threats, ensure data privacy, and maintain the integrity of their email communications.
To learn more about Wed to Seal and its capabilities, visit the official website.
4.7 out of 5
| Language | : | English |
| File size | : | 732 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 141 pages |
| Lending | : | Enabled |
| Screen Reader | : | Supported |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Top Book
Top Book Novel
Novel Fiction
Fiction Nonfiction
Nonfiction Literature
Literature Paperback
Paperback Hardcover
Hardcover E-book
E-book Audiobook
Audiobook Bestseller
Bestseller Classic
Classic Mystery
Mystery Thriller
Thriller Romance
Romance Fantasy
Fantasy Science Fiction
Science Fiction Biography
Biography Memoir
Memoir Autobiography
Autobiography Poetry
Poetry Drama
Drama Historical Fiction
Historical Fiction Self-help
Self-help Young Adult
Young Adult Childrens Books
Childrens Books Graphic Novel
Graphic Novel Anthology
Anthology Series
Series Encyclopedia
Encyclopedia Reference
Reference Guidebook
Guidebook Textbook
Textbook Workbook
Workbook Journal
Journal Diary
Diary Manuscript
Manuscript Folio
Folio Pulp Fiction
Pulp Fiction Short Stories
Short Stories Fairy Tales
Fairy Tales Fables
Fables Mythology
Mythology Philosophy
Philosophy Religion
Religion Spirituality
Spirituality Essays
Essays Critique
Critique Commentary
Commentary Glossary
Glossary Bibliography
Bibliography Index
Index Table of Contents
Table of Contents Preface
Preface Introduction
Introduction Foreword
Foreword Afterword
Afterword Appendices
Appendices Annotations
Annotations Footnotes
Footnotes Epilogue
Epilogue Prologue
Prologue Simon Spurrier
Simon Spurrier Cheri Schmidt
Cheri Schmidt Magdalena Wurth
Magdalena Wurth Ck Dawn
Ck Dawn Norma Budden
Norma Budden Carolyn Forche
Carolyn Forche Shifio S Patterns
Shifio S Patterns Richard Stokes
Richard Stokes Jean De La Fontaine
Jean De La Fontaine Mya Grey
Mya Grey Avishek Gupta
Avishek Gupta Jane Anne
Jane Anne Anne Applebaum
Anne Applebaum Timothy Dorr
Timothy Dorr Anne Doughty
Anne Doughty Homura Kawamoto
Homura Kawamoto Ryan Martinez
Ryan Martinez Emma Haslett
Emma Haslett Alice Finn
Alice Finn D Sean
D Sean
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Diego BlairFollow ·12.1k
Diego BlairFollow ·12.1k Nathaniel PowellFollow ·15.9k
Nathaniel PowellFollow ·15.9k Joseph ConradFollow ·2.7k
Joseph ConradFollow ·2.7k Clinton ReedFollow ·15.9k
Clinton ReedFollow ·15.9k Albert ReedFollow ·6.1k
Albert ReedFollow ·6.1k Gene SimmonsFollow ·4.6k
Gene SimmonsFollow ·4.6k Heath PowellFollow ·14.9k
Heath PowellFollow ·14.9k Mario BenedettiFollow ·17.5k
Mario BenedettiFollow ·17.5k
 Jared Nelson
Jared NelsonThe Da Vinci Code: A Literary Odyssey into the World of...
A captivating image of The Da Vinci Code...
 Harvey Bell
Harvey BellJohn Pearce: An Action-Packed Maritime Adventure
Join John...
 Ken Follett
Ken FollettSky Dragons: Unveiling the Majestic Creatures from the...
In the ethereal world of Anne McCaffrey's...
 Blake Bell
Blake BellEasy And Delicious Baking Recipes You Can Effortlessly...
Baking can be a great way to relax and...
 Maurice Parker
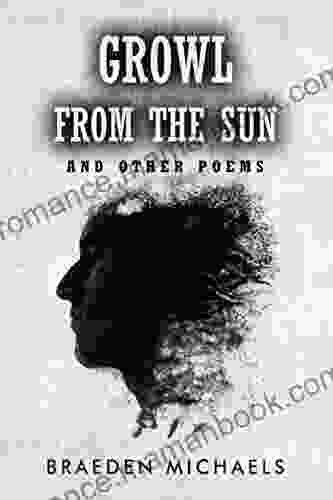
Maurice ParkerUnveiling the Profound Insights and Lyrical Beauty of...
In the realm of contemporary poetry, "Growl...
4.7 out of 5
| Language | : | English |
| File size | : | 732 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 141 pages |
| Lending | : | Enabled |
| Screen Reader | : | Supported |